Send Signal Messages with Kicksecure

Signal LogoHow-to: Use Signal Private Messenger with Kicksecure.
Introduction
[edit]Signal![]()
is a well-respected, free, open source, cross-platform encrypted messaging service. It supports individual and group messages (files, voice notes, images and video) as well as one-to-one voice and video calls. All communications are encrypted end-to-end for security, and mechanisms exist to independently verify the identity of contacts as well as the integrity of the data channel. The encryption keys are generated and stored at the endpoints (user devices), rather than by the servers. Both the client and server code is openly published, and the software is recommended by noted privacy advocates Edward Snowden and Bruce Schneier, among others. This is due to the strong architecture and limited metadata available in the ecosystem. [1] [2] [3]
The desktop application supports one-to-one voice and video conversations. [4]
This configuration allows the standalone Signal desktop client to link with the mobile device and send or receive messages from a laptop or desktop computer. [5]
Privacy
[edit]Broken Metadata Protection
[edit]Signal's metadata protection (who is communicating with whom) might be ineffective.
Hi, thank you for this thought provoking talk. You said so many things I disagree with it is tough to pick a question. But the one I want to ask is: The features that you have about private groups and sealed sender, those seem to be protecting data at rest for when the server is compromised the data that is on it is less useful to the attacker, but if the server is already compromised it is not really providing traffic analysis protection. Your metadata protection is effectively a pinky-promise oriented architecture and you have outsourced the keeping of the promise to a defense contractor owned by the richest man in the world; so my question is: How confident are you that Amazon is keeping the promises that you are making?
See this question and Moxie's (founder of Signal) answer here.![]()
Moxie failed to deny or refute this.
Amazon NSA collusion:
- NSA and Corporate Cooperation Revealed

- Ex-NSA chief Keith Alexander joins Amazon board

- NSA awarding its cloud contract to Amazon instead of Microsoft

Amazon is proud of its cooperation with law enforcement and providing them with recordings from Amazon Ring, the doorbell snitch. It is hard to believe they do not collaborate with higher agencies such as the NSA of the security apparatus ladder.
- Amazon Doubles Down on Ring Partnerships With Law Enforcement

- Amazon's helping police build a surveillance network with Ring doorbells

- Amazon Ring Gives Videos to Police without a Warrant or User Consent

- Amazon finally admits giving cops Ring doorbell data without user consent

- Amazon, Law Enforcement Joining Forces To Turn Your Front Door Into An Integral Part Of The Surveillance State

- Amazon's Free Doorbell Cameras Only Cost Law Enforcement Agencies Their Dignity And Autonomy

Prerequisites
[edit]Signal must already be installed on your Android or iOS device. First follow the download instructions![]()
on the Signal homepage if required. [7]
It is also recommended to create a separate Kicksecure that is only used for Signal because these instructions require the enabling of the Ubuntu Xenial repository for the desktop client. [8] The Signal developers do not maintain specific versions for other distributions, which is why Ubuntu is defaulted to.
Notices
[edit]Install the Signal Desktop Client
[edit]1 Notice.
- Kicksecure: Perform these steps inside Kicksecure.
- Kicksecure for Qubes: Perform these steps inside Qubes
kicksecure-18Template.
2 Add the Signal GPG key to the APT keyrings. [9]
To add the signing key, follow steps 1 to 4.
1 Securely download the key.
Select your platform.
Kicksecure
If you are using Kicksecure (kicksecure), run.
scurl-download https://updates.signal.org/desktop/apt/keys.asc
2 Display the key's fingerprint.
Optional for better security. If you are interested, click on Expand on the right.
gpg --keyid-format long --import --import-options show-only --with-fingerprint keys.asc
Verify the output.
- Digital signatures are a tool enhancing download security. They are commonly used across the internet and nothing special to worry about.
- Optional, not required: Digital signatures are optional and not mandatory for using Kicksecure, but an extra security measure for advanced users. If you've never used them before, it might be overwhelming to look into them at this stage. Just ignore them for now.
- Learn more: Curious? If you are interested in becoming more familiar with advanced computer security concepts, you can learn more about digital signatures here: Verifying Software Signatures
The most important check is confirming the key fingerprint exactly matches the output below. [13]
Key fingerprint = DBA3 6B51 81D0 C816 F630 E889 D980 A174 57F6 FB06
3 Copy the signing key to the APT keyring folder. [14]
sudo cp keys.asc /usr/share/keyrings/signal-desktop-keyring.asc
4 Adjust permissions on the signing key. [15]
sudo chmod 0644 /usr/share/keyrings/signal-desktop-keyring.asc
3 Add the Signal third-party APT repository. [16] [17] [18]
echo 'Types: deb URIs: tor+https://updates.signal.org/desktop/apt Suites: xenial Components: main Enabled: yes Architectures: amd64 Signed-By: /usr/share/keyrings/signal-desktop-keyring.asc' | sudo tee /etc/apt/sources.list.d/signal-xenial.sources
4 Install Signal.
Install package(s) signal-desktop following these instructions:
1 Platform specific notice.
- Kicksecure: No special notice.
- Kicksecure-Qubes: In Template.
2 Update the package lists and upgrade the system.
sudo apt update && sudo apt full-upgrade
3 Install the signal-desktop package(s).
Using apt command line --no-install-recommends option is in most cases optional.
sudo apt install --no-install-recommends signal-desktop
4 Platform specific notice.
- Kicksecure: No special notice.
- Kicksecure-Qubes: Shut down Template and restart App Qubes based on it as per Qubes Template Modification.
5 Done.
The procedure of installing package(s) signal-desktop is complete.
5 Done.
The process of installing Signal is complete.
Start Signal
[edit]To launch Signal, run.
signal-desktop
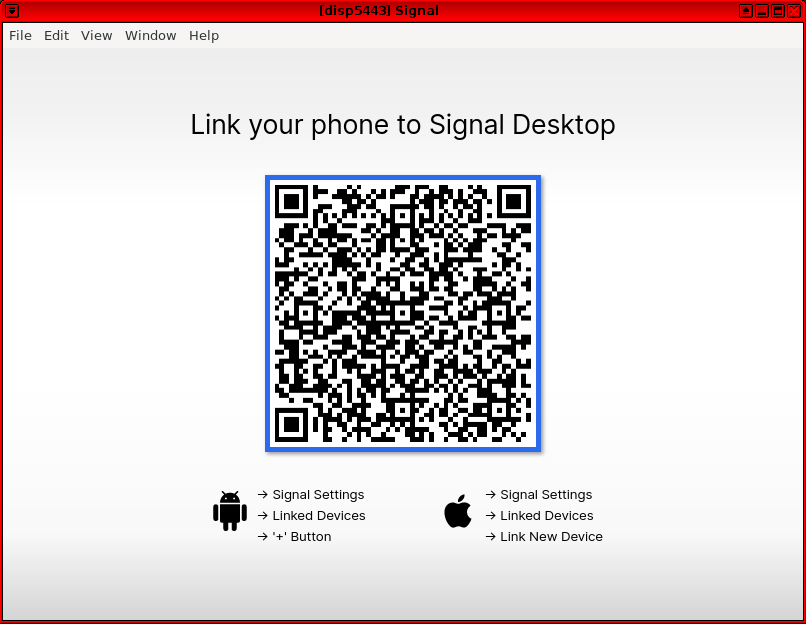
After launching the desktop client, it must be linked with the mobile phone. Be aware that messages are synchronized with Signal on the mobile phone.
Figure: Signal Desktop in Kicksecure
Claims That Signal Encryption Is Broken
[edit]Cellebrite![]()
formerly claimed
![]() they were able to decrypt Signal encryption. However, the article details were later removed [19] because it was debunked by Moxie Marlinspike
they were able to decrypt Signal encryption. However, the article details were later removed [19] because it was debunked by Moxie Marlinspike![]()
(xcancel
![]()
) (co-founder and currently CEO of Signal Messenger), Edward Snowden
![]()
(Nitter
![]()
), and Filippo Valsorda
![]()
(Nitter
![]()
). Signal also officially
![]()
responded to this false claim.
Note: cryptographer Bruce Schneier wrote an article about this issue in his blog entitled "Cellebrite Can Break Signal", but he later apologized![]()
for his erroneous post.
Signal Delayed Updating Their Server Code in Time
[edit]
Signal server code was delayed![]()
in being updated to prevent spammers from gleaning the new anti-spam measures the company planned to enact (according to the previous
![]()
Signal CEO Moxie Marlinspike [20] [21]).
See Also
[edit]Footnotes
[edit]- ↑
https://en.wikipedia.org/wiki/Signal_%28software%29

- ↑
For additional Signal features, see: Wikipedia: Signal (software) - Features

- ↑
Signal blog

:
By design, Signal does not have a record of your contacts, social graph, conversation list, location, user avatar, user profile name, group memberships, group titles, or group avatars. The end-to-end encrypted contents of every message and voice/video call are protected by keys that are entirely inaccessible to us. In most cases now we do not even have access to who is messaging whom.
- ↑
https://github.com/signalapp/Signal-Desktop/releases/tag/v1.35.1

- ↑
https://www.signal.org/blog/standalone-signal-desktop/

- ↑ The number can be different from the device's SIM card; it can be a landline or VOIP number, so long as the user can receive the verification code and possesses a separate device to set up the software.
- ↑ Also see: Installing Signal

.
- ↑ Common advice is to not mix repositories from related distributions like Ubuntu and Debian, since this can cause system instability.
- ↑
https://github.com/freedomofpress/ansible-role-signal-desktop

- ↑
Using Qubes UpdatesProxy (
http://127.0.0.1:8082/) because Qubes Templates are non-networked by Qubes default and therefore require UpdatesProxy for connectivity. (APT in Qubes Templates is configured to use UpdatesProxy by Qubes default.)
- ↑
Even more secure would be to download the key Disposable and then
qvm-copy
it to the Qubes Template because this would avoid
curl's attack surface but this would also result in even more complicated instructions. - ↑
Even more secure would be to display the key in another Disposable because this would protect the Template from
curl's andgpg's attack surface but this would also result in even more complicated instructions. - ↑ Minor changes in the output such as new uids (email addresses) or newer expiration dates are inconsequential.
- ↑
https://forums.whonix.org/t/apt-repository-signing-keys-per-apt-sources-list-signed-by/12302

- ↑
This is necessary because the umask set in Kicksecure will result to the file permissions of the copied file being set to
0640, which will prevent them from being read by non-root users. - ↑
https://signal.org/download/

- ↑
https://forums.whonix.org/t/apt-repository-signing-keys-per-apt-sources-list-signed-by/12302

- ↑
See this for a comment why
tor+is useful even inside Kicksecure. - ↑ https://www.cellebrite.com/en/blog/cellebrites-new-solution-for-decrypting-the-signal-app/

- ↑ https://github.com/signalapp/Signal-Android/issues/11101#issuecomment-815400676

- ↑ https://www.xda-developers.com/signal-updates-public-server-code/#update1


We believe security software like Kicksecure needs to remain Open Source and independent. Would you help sustain and grow the project? Learn more about our 14 year success story and maybe DONATE!